Please let me start this blog by saying these are my personal views of the various competitions and in no way reflect the opinions of Cyber Skyline or the National Cyber League (NCL) or any of the other Player Ambassadors for that matter. As an educator, I tend to have a slightly different take on the competitions than a standard coach. I am always looking for the educational value or the gain for my students within any competition. There must be educational growth or, in my opinion, the competition is not worth the effort.
Firstly, I’d like to talk about the website CTF Time. It’s a great place to find out what’s going on in the cyber competition community and provides great links to write-ups and sign-ups. Another great place to look is Major League Cyber. These two websites, and I’m sure there are a lot more, should allow you to find what’s out there with regards to cyber competitions and how to keep your teams busy during the ‘downtime’ between the major competitions, most of which I will cover in this blog.
Cyber Patriot
“At the center of Cyber Patriot is the National Youth Cyber Defense Competition, which pits teams of high school and middle school students in the position of newly hired IT professionals tasked with managing the network of a small company. Through a series of online competition rounds, teams are given a set of virtual operating systems and are tasked with finding and fixing cybersecurity vulnerabilities while maintaining critical services. The top teams in the nation earn all-expenses-paid trips to Maryland for the National Finals Competition where they can earn national recognition and scholarship money.”
Air Force Association
Above is the official statement from the Air Force Association (AFA) with regards to the annual Cyber Patriot competition, now in its 11th year. I’ve been coaching it for eight years. Amusingly called Cali Patriot, due to the outrageous number of teams from California that do incredibly well at this, this is primarily a blue team competition. If you are unfamiliar with the red/blue team concept, it means it is a purely ‘defensive’ cyber activity.
Students are given compromised virtual machines of various operating systems, these include Windows Desktop, Windows Server, various flavours of Ubuntu Linux, and finally, the last nail in the coffin when Debian comes along. The competitors spend six hours attempting to find and rectify these issues and answer some forensics questions that can be part of the scenario. A lot of Cisco curriculum with tests and simulations using Cisco’s packet tracer software is thrown in for good measure.

Above is an example of the kind of desktop your team will be presented with. Each round has a different scenario based on misc. topics including superheroes, cartoons, books, etc. The readme on the desktop outlines the majority of the tasks the student have to perform, but not all of them. During later stages of the competition, things like removing unwanted software become somewhat harder as the system will have locked participants out of the control panel, among other hurdles. In later parts of the games, it becomes a deeper dive into the internals of Windows before you can start some of the more basic tasks.
Scoring is automatic with a scoring system that plays a little tune when you accrue points and a siren when you do something you shouldn’t and lose points.
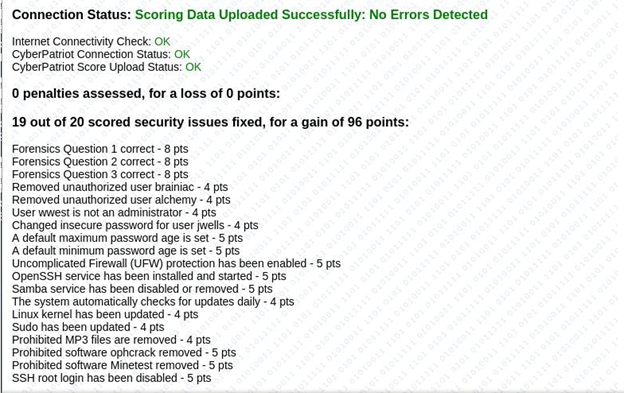
Above is an example of the scoring report. Notice that the system tells you how many problems you are attempting to fix in each round for each system.
Now for my personal view of this competition. As I said before I’ve been coaching my team for the past eight seasons and we’ve managed to do quite well for ourselves given that we are a very small school. Initially, schools struggle with this competition. It’s very resource-heavy with each team requiring three to four reasonably specked machines to run the virtual machines (VMs) and an additional one to run packet tracer. Secondly, the on-ramp for this competition is quite high and, although the AFA does a good job with resources such as learning materials and practice rounds that coaches have the answers to, it’s potential for educational growth to me feels very small. The AFA does produce a “crib sheet” of vulnerability categories at the end of each round, but it is done in such a cryptic manner that teams who are struggling will continue to struggle and unfortunately drop out. All in all, it’s a good beginner competition for those that want to start in Cyber Competitions, but I think its long term appeal is limited due to the small problem space it has to work in.
Below is a quote from one of my students about their CyberPatriot experience:
I’ve competed in CyberPatriot for two years, and it’s an experience unlike any other. I came into my first year of competition with absolutely no experience, and while I didn’t perform as well as I would’ve hoped, but I learned more about cybersecurity than I could’ve dreamed of learning in just a few short days. I was able to connect with people that taught me more about the subject, and I was able to realize that I wanted to pursue cybersecurity as a career. It’s certainly difficult, and I’ve had more than one round that ends with me banging my head on a table, but in the end, it’s all worth it. CyberPatriot is a competition in which I can spend time with my friends and do something I love, all while learning about my future career. It’s a great experience, and I can’t wait to compete again.”
Molly Shapiro, Padua Academy 11th Grader
picoCTF
“picoCTF is a free computer security game targeted at middle and high school students, created by security experts at Carnegie Mellon University. The game consists of a series of challenges centered around a unique story line where participants must reverse engineer, break, hack, decrypt, and do whatever it takes to solve the challenge.”
Above is the official description of the picoCTF competition, which is now in its seventh year. It’s a pretty familiar CTF format, but what I like about it is the variety of categories within the competition.
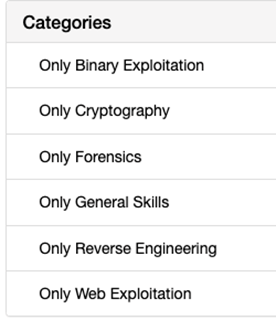
From an educational point of view, this competition ticks a lot of boxes. A great variety of fields are covered, allowing teams to specialize. It’s free, which is a big plus for schools that are strapped for cash. It’s resource requirements are a lot lower than other competitions. That being said, since my school is a Mac school, we have problems with the requirements for some tools used in competitions.
Also picoCTF has the honour of having what I consider to be most evil problem I’ve ever come across called ‘Shark on a Wire 2’. I won’t give it away, but I’ll just to say, if you like packet analysis with Wireshark, you should check this out because you’ll kick yourself once you get it. I also have a soft spot for any competition that has a Forensic category. There is something about Forensics that always piques my interest. Another good thing about this competition is that the people who run it don’t seem to mind about very comprehensive write-ups being released. From an educational point of view this is fantastic, it allows students to learn new skills whilst applying them to known problems in preparation for next years competition.

Above is a screenshot of the interface for picoCTF. It’s very crisp but could be considered a little plain, especially when compared to the next competition I’m going to cover, but what it lacks in aesthetic it makes up for in play-ability. I also feel that picoCTF requires a far broader skill set than other competitions. Once the actual competition is done, the hosts leave the problems up for competitors to continue to learn.
Below is a quote from one of my students about their picoCTF experience:
“picoCTF was a ton of fun. I especially liked the variety of each type of challenge (cryptography, web exploitation, etc). The game portion of it was cool, too; even though it wasn’t worth a whole lot of points to solve all the extra puzzles, it served as a good mental break from completing the challenges. There were some problems/inconsistencies in a couple of the challenges, but most of them were fixed before the end of the competition and they didn’t take away from the experience. Overall, picoCTF was a really fun way to brush up on some classic CTF skills while also learning new techniques.”
Annamarie Warnke, Padua Academy 11th Grade
Girls Go CyberStart
“High school girls will master new skills while working their way through a vast online training game and battling for cash prizes! Take part on your own or join a Club to compete alongside friends.”
Above is the official description of the Girls Go CyberStart competition, it’s specifically aimed at girls in high school, although the girls can win licenses for the boys in their school to play the game, but guys cannot compete officially. It’s produced by SANS, who also runs the Cyber Fast Track competition aimed at college students.
The game consists of “Assess”, a mini-competition consisting of 15 problems for girls to solve to allow competitors to move forward to the “Game” portion of the competition. From there, four teams are allowed into the “Compete” section, which is considered to be the national final. From the outset, Girls Go is very pretty on the eyes and consists of four bases.
A headquarters, which requires more general cyber skills, web application exploitation, cryptography, etc. A forensics base that introduces girls to tools such as Autopsy to analyse captured disk images and memory dumps. The moon base is wholly devoted to girls developing skills for programming in Python. Lastly, there is a volcano base which none of my students have managed to open, so I have no clue what is back there.
Each level within a base has several problems to be solved before you can progress, each level is a scenario in its own right.

Above is an example of a scenario description for a level and below is an example of a problem.

The year is the third year of the competition and it is becoming a very polished competition. I like the variety, although unlike picoCTF I’ve yet to see any write ups about previous years competition. Like picoCTF, it’s free and a Manjaro Linux VM is included for students to use.
One last point about the competition is that SANS realised that some students lacked the access to appropriate technology to be able to compete, so they developed a cloud version of Manjaro to allow students to compete via lower powered devices such as Chromebooks.
Below is a quote from one of my students about their Girls Go CyberStart experience:
“Girls Go Cyberstart was the first CTF I participated in, and it really sparked my interest in Cybersecurity. The challenges start out really easy, so even someone with no experience can complete some challenges, especially with the help of the Field Manual. There are so many challenges that some of them start to get a little repetitive, especially in the middle levels, but overall the challenges do a good job of building off of each other. Additionally, CyberStart Assess and CyberStart Compete change up the type of challenges, so nothing gets too stale. Since CyberStart is open for so long and has so many components, it a great opportunity for me to really hone techniques that can often be useful in other CTFs.
Annamarie Warnke, Padua Academy 11th Grade
National Cyber League
“In 2011, a group of cybersecurity-focused academics from several public agencies got together and created an innovative way for students to apply what they were learning in class. It would be important to reduce barriers and excite young people to participate. Students would have easy access, no matter what their age, skill level or location. The NCL Competition was born. It was one of the earliest e-sports – a competitive game-meets-edutainment – and it would simulate real-life cyberthreats in a safe environment, for students to learn how to defend organizations against cyber-threats and keep them secure.”
Is it a CTF or is it an ‘e-sport’, the National Cyber League (NCL) is the one of the longest running CTF competitions out there, running two seasons a year, individuals first then a team event, this competition is a really polished event. The NCL boasts its gymnasium where competitions can ‘train’ before the big day and the all important ‘scouting report‘ that shows a competitors accomplishments and more importantly a learning curve over time. From a collegiate perspective, this is the ‘big win’ for this CTF, as far as I know, its the only CTF to gain respect amongst the professional community, and added to this the Cyber Skyline platform is used by companies as a testing range for potential employees you are going to get noticed if you do well in this CTF.

Above is a screen shot of what you can expect the types of challenges are going to be, sadly missing the Forensics challenges offered by some CTFs, but what its lacking in that category, it makes up for in others. No other CTF has a pure OSINT category which is another favourite of mine and the quality of the challenges makes the event fun and leaves you wanting more

As you can see from the screenshot above, the OSINT category of Cyber Skylines ‘professional’ offering as you can see there is a wide degree of difficulty of problems allowing newcomers to get their feet wet and more seasoned competitors a chance to push their skills.
Unlike any other CTF that I know of, NCL has a team of dedicated Player Ambassadors, like yours truly, who are constantly trying to help their players succeed in the NCL Games. As you can see from the line-up below, these NCL Superheros are here to save the day when you just don’t know where else to turn. It’s a truly unique offering from a CTF.

Downsides, it’s the only CTF that costs money but at $35 per competitor it’s not going to break the bank, (Cyber Patriot costs $300 per team, unless you are an all girl team then its free) and given training factor the gymnasium brings its worth it for the educational gain.
In summary, there are a lot of GREAT competitions out there for students to be able to gain more exposure to different fields in Cyber, so use them to your advantage as much as you can.
