HOW DO PASSWORDS WORK, AND WHAT IS A HASH?
Generally when you create a password for an online account, your password is run through a one-way encryption algorithm called hashing, and it is this resultant hash that is stored on the server. When you later go to log into the site and type your password in, whatever password you type is hashed, and then the hash is compared to the hash stored on the server. If they match, it is assumed you must have typed in the correct password. The server host should have no idea what the password actually is, only the resultant hash.
A brute force attack would simply try every single possible character combination, try hashing it, and then check to see if the hash matches what is on the server. Servers mitigate this by restricting people to, say, 3 attempts within a 15-minute period. Being limited to 3 attempts in 15 minutes will slow down a brute force attack to where it’s no longer a reasonable attack. However, if the stored hashes were stolen, then an attacker could sit at home and try to find a combination that matches the hash on their home computer with no time limits in place. That is what we are doing when we’re in cracking competitions—we have the hash and the opportunity to throw as many attacks at it as we can until the competition is over.
Throughout this tutorial, I will be using Windows. If you’re on Linux, the commands run the same, apart from just the normal flipping of \ / in pathing and dropping the .exe from the command. Otherwise, the parameters and options are all the same.
Taisa here! Still not sure how hashing works?
The best explanation of hashing that I ever read was in The Cuckoo’s Egg, a true story of 1980s computer espionage by Cliff Stoll.
Chapter 7:
In 1975, Bob Morris and Fred Grampp of Bell Laboratories developed a way to protect passwords, even when files weren’t secure. They would rely on encryption, rather than file protection. If you choose the password, “cradle,” the computer doesn’t simply store your choice into a file of passwords. Instead, Unix scrambles the letters into an encrypted word [a hash], say, “pn6yywersyq.” Your encrypted password [the hash] is stored, not the plain text.
So a Unix password file might look something like this:Aaron: fnq24lkcvs
Blacker: anvpqw0xcsr
Blatz: pn6yywersyq
Goldman: mwe785jcy12
Henderson: rp2d9c149b7
Following each account name is the encrypted password [the hash]. Like Wayne said, stealing the password file just gives you a list of people.
The computer program that encrypts [hashes] “cradle” into “pn6yywersyq” is built upon a trapdoor algorithm: a process that’s easy to do, but difficult to undo. When Sally Blatz logs in, she types in her account name, Blatz, and then her password, cradle. The system encrypts [hashes] the password into pn6yywersyq, and compares that to the entry in the password file. If the encrypted entries don’t match, Sally is booted off the machine. The plain text password itself isn’t compared, its encryption [hash] is. Password security depends on the trapdoor function.
Trapdoor functions are mathematical ratchets: you can turn them forwards, but not backwards. … To makes these locks pickproof, it’s got to be impossible to reverse the algorithm. …
Wayne and I had watched the hacker break in and steal our password file. The hacker now knew the names of a few hundred scientists. He might as well have asked for our telephone book—at least that included addresses. Unless he owned a Cray supercomputer, he couldn’t invert the trapdoor function, and our passwords remained safe.
Chapter 28:
This was the second time he’d ripped off my password file. What for? There’s no key to unlock these encrypted passwords [hashes]: they’re just goulash until they’re decrypted. And our encryption software is a one-way trapdoor: its mathematical scrambling is precise, repeatable, and irreversible.
Did he know something that I didn’t? Did this hacker have a magic decryption formula? Unlikely. If you turn the crank of the sausage machine backwards, pigs won’t come out the other end.
At least, that’s how hashing is supposed to work! We now return you to your regularly scheduled post from ghostinth3machine for an explanation of how hashcat can be used to turn cryptographic sausage back into a pig on the Cray supercomputer of today—your laptop.
IDENTIFYING HASHES
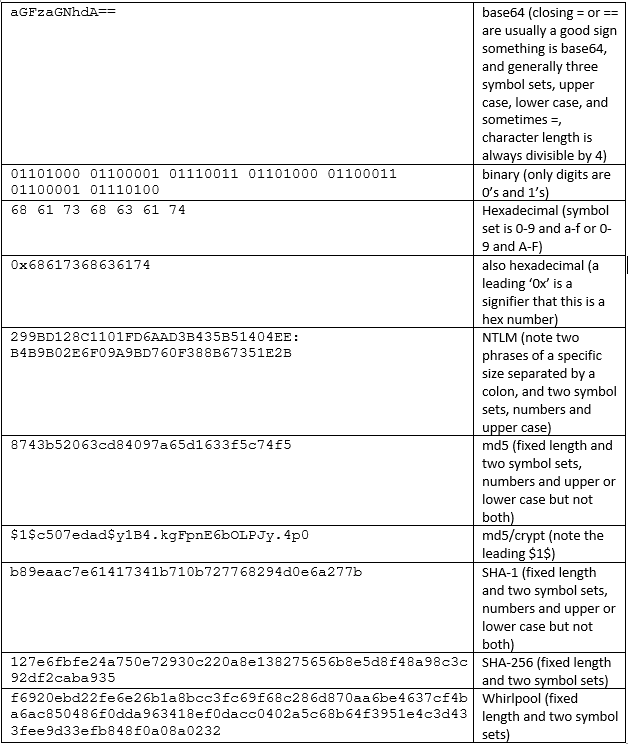
Each hash type is always of a predetermined length, and different ones may use different character sets or leading digits, like how md5/crypt is recognizable by the leading $1$. In time, a lot of these will be recognizable at a glance. Hashcat offers an example guide which is a very handy reference, and there also exist software alternatives that will make a best-guess at what type of hash a certain hash is. This guide is also helpful because once you identify the hash, it tells you what attack method to use in Hashcat. You can search “what type of hash is this” in your browser, and multiple online hash checkers will appear. If you receive a Token length exception, that is a sign that the type of hash you are trying to crack does not match the -m identified hash in Hashcat.
COMMAND STRUCTURE
The command structure for Hashcat is as follows: the Hashcat command, followed by parameters, followed by the hash (which can be a single hash or a file containing multiple hashes of the same hash type), followed by any dictionaries or masks. Depending on your video card, you may need to use the --force option to suppress error messages, as not all video cards work seamlessly with the hash kittie. Hashcat commands will follow this structure:

ATTACK MODES
There are five basic attack modes.
-a 0is a straight/dictionary attack, which uses a wordlist.-a 1is a combination attack, which uses two wordlists which Hashcat will combine into one.-a 3is a brute force attack, very slow and really just trying every single possibility there is.-a 6is a wordlist + mask attack-a 7is a mask + wordlist attack
If you don’t choose anything, it will default to -a 0.
METHODS
Hashcat does not automatically determine what type of hash it is cracking. You have to manually identify the hash and select the appropriate method. If you do not select a method, it defaults to -m 0 and assumes you are trying to crack an md5. This list contains examples of the different types of hashes so you can try to identify them, as well as listing which method is associated with that particular hash.

DICTIONARIES
Dictionaries are just text files with a list of words. Dictionary attacks are going to use the words in a particular dictionary as the basis for generating passwords and then comparing the hash of that password against the target hash. You can create your own custom dictionaries or even go looking for pre-existing ones. Skull Security has a nice collection of pre-made dictionaries. Rockyou.txt is a particularly famous dictionary—it’s a famous password dump from long ago but is useful in that it’s a dictionary of actual, real-world passwords, and people are infamously bad about using passwords more complex than that.
If you’re using Kali, you can find rockyou preinstalled at /usr/share/wordlists/rockyou.txt.gz—just keep in mind that it is compressed, and you will need to unzip it first before you can use it: sudo gzip -d /usr/share/wordlists/rockyou.txt.gz
MASKS AND CHARACTER SETS

Masks are useful when, for example, you know a password starts with 3 digits, or ends with 4 digits. -a 6 is the attack mode that says to try the mask at the end, while -a 7 tries the mask at the beginning. Using a character set will try every single character in the set. Using the character sets in the above picture, we could create a mask attack such as:
hashcat64.exe -a 6 hash.txt rockyou.txt ?d?d
which says to try everything in rockyou and append every possible set of two digits to the end.
hashcat64.exe -a 7 hash.txt ?d?d rockyou.txt
which says to try everything in rockyou and prepend every possible set of two digits to the beginning.
OTHER PARAMETERS AND RULES
Some other useful parameters are:
-oto designate an output file where the cracked hashes will be stored. Keep in mind this will only store the cracked password, not the hash that went with it, so if you’re cracking more than one password at a time, it’s easy to confuse which is which. Hashcat will keep ahashcat.potfilewhich is simply a text file of collected hashes and passwords combined that you have already cracked. When you try to crack a password, Hashcat will check the potfile first to see if you’ve already done it before, to see if it can skip the processing to recrack it.--forcewill suppress error messages related to video cards and may very well be necessary.-gwill apply a randomly generated set of rules.-rwill use a particular rule set. Keep in mind, too, you can use multiple rules. Just prefix each with-r, and they will interact with each other, though this can exponentially increase the number of possibilities Hashcat will try.
Generally speaking, if you’re starting out, you’re going to want to use pre-made rules rather than creating one yourself. If you are interested, https://hashcat.net/wiki/doku.php?id=rule_based_attack describes how to create your own rules, and here you’ll find a small, curated collection of pre-made rules, including best64.rule, dive.rule, and leetspeak.rule.

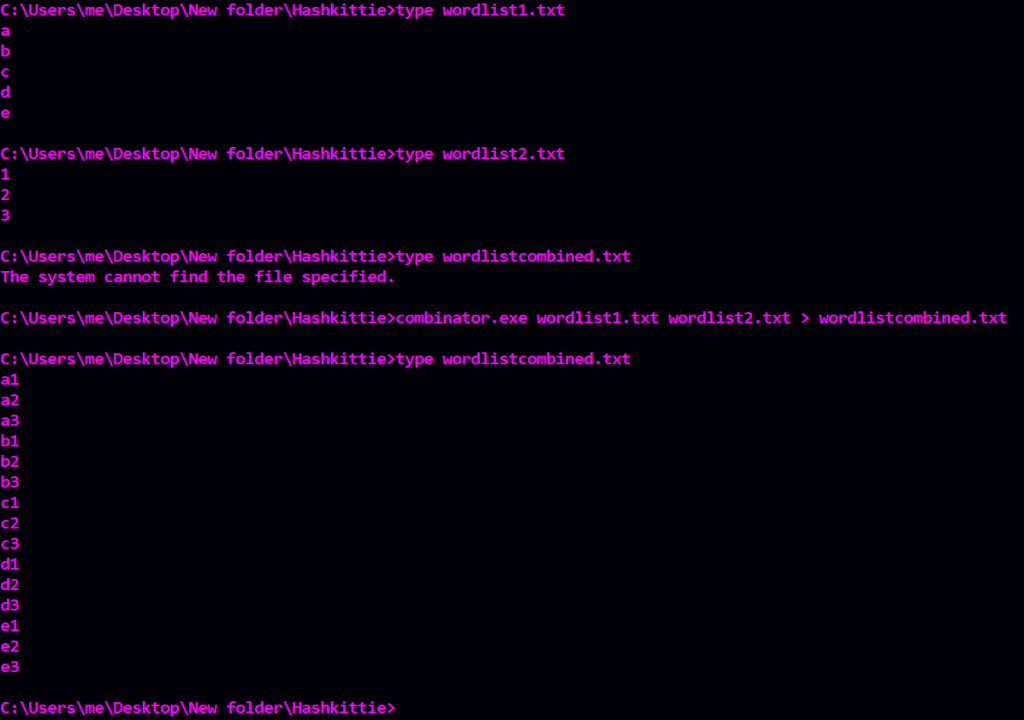
HASHCAT UTILITIES
Hashcat also has several utilities available as a separate download here. Of these, the ones I find most useful are cap2hccapx, which is used for altering an encrypted pcap into a file that Hashcat will recognize and attempt to crack, and combinator, which is useful for combining two wordlists into one as opposed to doing a combo attack, which would attack with two separate wordlists.


HASHCAT GUI
If you’re on Windows, there is a front-end GUI available here. This gives you a point-and-click interface which makes it easy to select all of the options you are looking for.
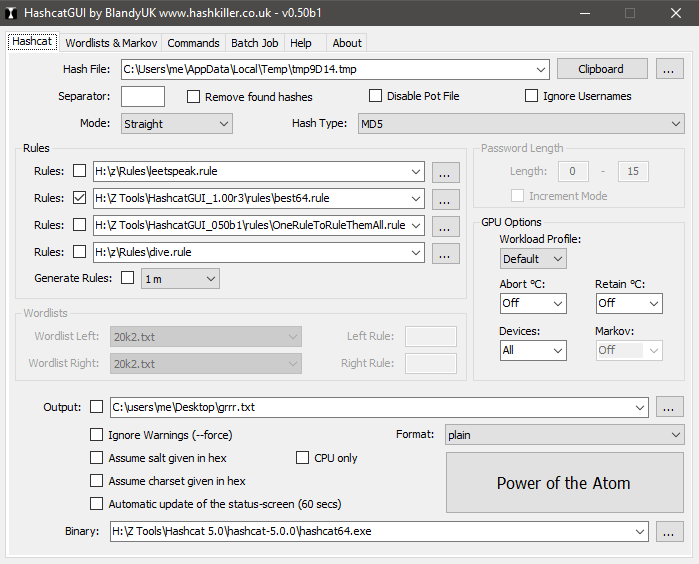
If you use the GUI, one thing to keep in mind is that if you’re going to crack from the clipboard, pay attention to white spacing in the hashes you paste.
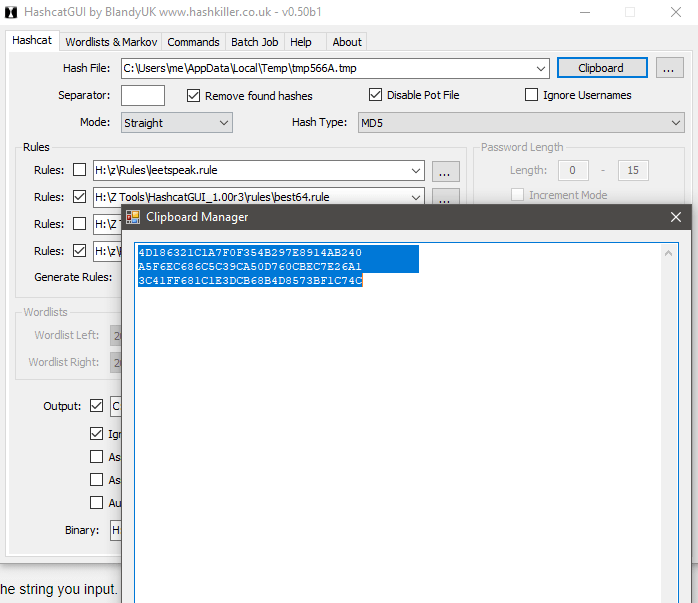
White space makes a difference and should be deleted.
One nice aspect of the GUI is, as you’re learning Hashcat, there is a Generate Command tab which will generate the actual CLI command you would type with the options you have selected. This is a great reference to look at as you are learning the command line.

(As a side note, I realize the GUI from the screenshot is an older version advertising the old link; https://hashkiller.io/download is the current site.)
