Oh, the news about a new Forensics category in the National Cyber League (NCL) Games blew all of us out of our seats. That’s right, we get a new category! Wait, but what is forensics? Let’s dive in and get a glance at what we can potentially run into with this shiny new category.
*Disclaimer: The NCL Player Ambassadors have NO IDEA what this category’s challenges will look like. Just like you, we will be seeing these for the first time in the Fall 2020 season.*
Long ago, in a far away land… wait, wrong story! Back in the early 1990s, I had my first encounter with forensics. The hard drives in that time were not those tiny lightweight devices that you see today, but rather clunky. Why did I choose the word clunky? Oh, that’s the noise they’d make when they were dying. Clunk, click, tink, growl (yes, it growled at me!)… uh-oh, I have data on there that I can’t lose because I didn’t back it up! It’s okay, I can still fix this, I’ll throw the hard drive in the freezer for a bit then run Norton Ghost on it to make a copy and then extract the data…
Okay, first allow me to explain that, yes, I absolutely did this, as did others. What we need to know is that forensics itself entails several aspects. It’s not only looking at, or retrieving, the data that has been corrupted or wiped out completely, but also preserving it and documenting your findings in a usable manner that, if needed in court, can be presented properly.
With the Forensics category being new, I personally have not had the privilege of seeing what we’ll be doing and will be experiencing it for the first time along with all of you out there in CTF land. With that being said, I will speculate what could potentially be there, and we’ll all go on this ride together!
Simply put, digital forensics is the recovery and investigation of information found in digital devices. Now, from this perspective it can seem to leave a very wide arena of what we might see. For instance, much like my opening statement, the frozen hard drive. For the record, no, I do not think we’re going to be freezing a hard drive.
Given what forensics is, and knowing that even wiping a hard drive still leaves trails of information that can be extracted and sometimes restored to see what was deleted, intentionally or not, we have learned at some point that data is never truly fully gone. One of the first forensics tools that I personally used was OnTrack Easy Recovery. Then, I used Hiren’s Boot disk quite a bit. It was a boot-able recovery tool built with Windows PE.
Back when I was first introduced to the magic of being able to recover data, this usually just meant hard drives, tape drives, any storage media that was local. With the progress of technology, there had to be a change in how digital forensics was handled to keep up. Now, this does not just mean storage media, it also covers network and internet connections, mobile devices, IoT, and literally any device that can store, access, or transmit data.
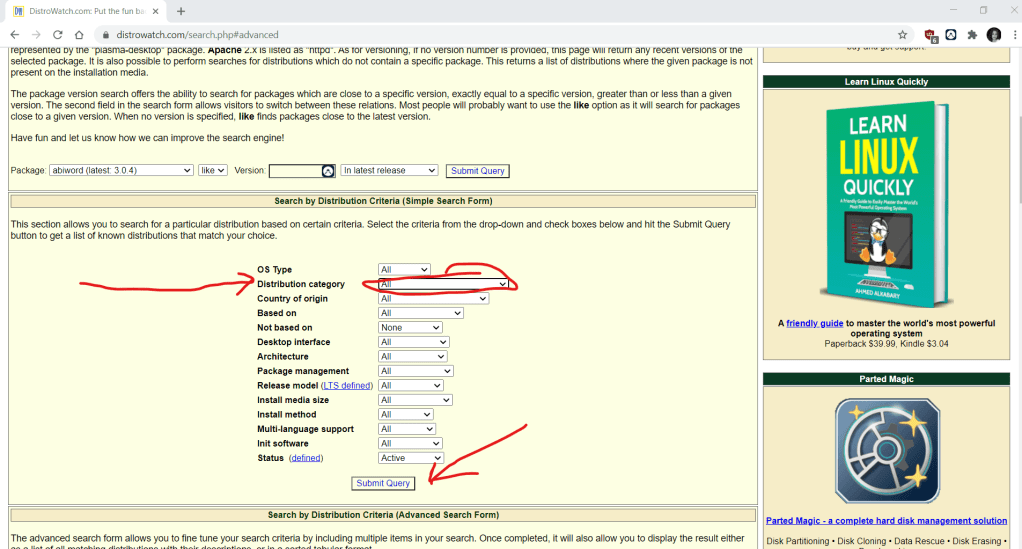
I use Kali Linux, like a lot. I’m telling you this because most of the tools are already included. There are other Linux distributions that focus on specifically forensics—for example, Computer Aided Investigative Environment (C.A.I.N.E.). You can filter out the type on distrowatch.com to show only forensic based versions.

NIST developed a Computer Forensics Tool Testing (CFTT) that gives us a guideline of tools that were tested, and it publishes results. What we might expect to see could be any of the following:
- Deleted files
- Deleted partitions
- Registry deletion or corruption
- Raw disk images
- Photo and video recovery
- Secure wiping
- Write protection
That all being said, I also suspect that Cyber Skyline may have some tricks up their sleeves to allow you to do all the work you need within the web browser and Game platform.
Look for more posts about Forensics after this Fall Season when we all have had the chance to experience it to give more detailed reports!
