Readme.md
Before we get into the tips and tricks that you have been promised, there are a few bases that should be covered first, to ensure you are able to get the most out of these wonderful tips and tricks.
First, if you have not yet had the chance, read Jeana’s first blog on wireless access exploitation, which can be found here! Jeana defines this category, as well as a high level of what you will need to complete the task and an introductory tutorial of what is covered during the National Cyber League (NCL) Games with wireless access exploitation. If you have not completed the segment on what you will need to complete these challenges, read John “Mako” McGill’s blog or Hush1e‘s blog on how to download, install, and begin running Kali.
Once you have completed the two requirements above, you will likely want to verify that the tools you need function correctly, so go ahead and start up your Kali VM.
Step 1: Click on applications in the top left hand corner.
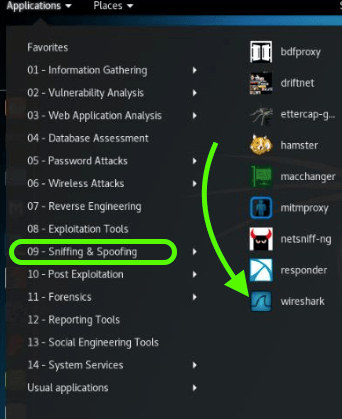
Step 2: Select menu 09 – Sniffing & Spoofing
Step 3: Click on your friendly neighborhood packet sniffer, Wireshark, and patiently wait 10-20 seconds.
Great! Wireshark works, now, it’s time to verify aircrack.

- Click on terminal.
If you haven’t played with this yet, or are just experiencing the command line for the first time, may I introduce your new best friend? This is terminal. When you give it commands, it does things. Sometimes, it does stuff, like aircrack. - Type aircrack-ng help to verify it runs.
- Celebrate by continuing to read this post.

(Yes, this is me as a parrot, and yes, this is what I do when excited during the games)
The Tips
(What You Actually Came Here to See)
- Always run aircrack with a target file, otherwise, aircrack cannot crack.
Aircrack-ng -l FILENAMEHERE.cap
- Always remember to determine the network that aircrack needs to target by selecting a number.
- Determine the encryption protocol for which you will need the key. WEP vs. WPA. If the encryption is WPA, jump to further down this list for the base commands and a few suggestions
- Let the cracking process run. For WEP, you only need to be mildly patient
- Whenever you’re running aircrack, take a quick stretch break and stop starring at your screen for a few precious moments.

- Verify that aircrack returned a KEY FOUND! Message with a key either in Hex or Ascii.
- Celebrate (again) I would advise a snack this time. Never forget to eat while competing. It’s not a fun time.

REMEMBER: WPA and WPA 2 cracking takes more effort
- Run aircrack with the target .cap file as well as the flag for wordlists (-w) I would suggest starting with rockyou as it comes standard with Kali and lives in /usr/share/wordlists/rockyou.txt
aircrack-ng FILENAMEHERE.cap -w /usr/share/wordlists/rockyou.txt
- Get some tea, and watch an episode of your favorite 44 minute TV show, or read a few chapters of your favorite Harry Potter book.
- Be patient, this may take up to two hours, pending your specifications.
- Wash rinse and repeat with different wordlists until you find what you need.
- Don’t give up. Pull down other wordlists if needed or generate one if the challenge requires it!
- Celebrate one last time! You did it!!
Lastly, if everything above fails, documentation is your friend.
