With the National Cyber League’s (NCL) 2017 Spring Preseason starting tomorrow, I wanted to post this list for both my team at Pace University and the team I am coaching at Westchester Community College.*
To both my teams, I hope you’re having fun getting ready for the preseason game. If you haven’t checked out the online training gymnasium that NCL provides, make sure you do! They have some great practice material!
But first things first.
What is the NCL?
The National Cyber League (NCL) is a national collegiate cybersecurity competition. With its puzzle-base, capture-the-flag style competition, this virtual training ground allows college students to prepare and test themselves against real-life security challenges they will likely face after graduation.
One of my favorite characteristics of the NCL competition is that all participants are able to try challenges of Easy, Medium, and Hard complexity in any section of the game which allows students to really shine in the areas they excel. This is especially important since top companies pay to have access to the NCL scouting reports after the season ends.
The NCL Season is broken down into three parts: Preseason, Regular Games, and Postseason. Each is unique in their own way.
Preseason is an individual competition that allows the NCL to assess participants to determine their current skill level. After the preseason, participants are placed into one of three brackets: Gold, Silver, and Bronze. This allows students to compete with other participants who are at a similar skill level.
Then the regular season begins. In my previous experience, there were 2 regular season games, but for the 2017 Spring Season (the first full spring competition), there will only be one regular season game. This is when your scores matters. You will be ranked both overall and within your bracket. This is your last chance to shine individually before the postseason.
During Postseason, you will compete in teams of 5-10 participants. This is definitely the best part of the competition for new participants. Personally, I learned almost everything I currently know from working in teams during the postseason. I had an amazing partner my first season. He and I worked so well together that we were co-captains of the entire Westchester Community College Cybersecurity Club’s NCL team which consisted of 37 individuals and 3 teams in post-season last semester.
Sounds good, but what do we do now?
Preparation
The first thing I do is set up my virtual machines. I exclusively use virtual machines during the competitions as some files may contain potentially harmful software. NCL does its best to duplicate real-life scenarios. That sometimes means having links to active viruses and malware. During the Fall 2016 Preseason competition, they issued the following warning on one of their Network Traffic Analysis challenges:
“This packet capture contains malware and may be flagged by an antivirus. You do NOT need to execute the malware to complete the challenge. Take appropriate measures to ensure your safety.”
So please, do as they say, and take appropriate measures to ensure the health of your computer. For me, that means using VMs.
About My VMs
You don’t need an extensive virtual machine set up. I simply set up one VM with Windows 7 or later and another with Kali-Linux. For the Windows VM, I always install several tools. For brevity, all the tools will be listed below. With Kali, the only thing I need to install is the updates. If you have questions about how to set up either virtual machines, I’ve linked to some of the Youtube tutorials I think will be helpful.
VMWare Workstation Install
Windows VM Install
Kali VM Install
And without further adieu, the list of the tools that I use for each section of the NCL Challenges.
My Toolkit
For Open Source Intelligence

The Open Source Intelligence challenges are like an open book test where the book is the entire internet. It’s a great place to START! Wrack up some fairly easy points early on and feel good knowing you will rank higher than all of other people who didn’t even log in to try. Take that, resume!
For Image Metadata Extraction
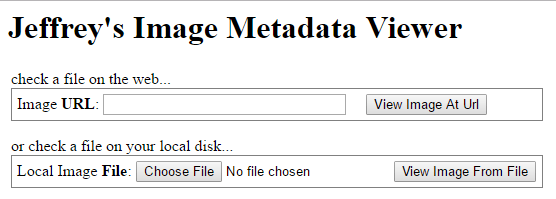
I use both Irfanview and Jeffrey Friedl’s Image Metadata Viewer. Irfanview requires an installation. Jeffery Friedl’s is online. Both will show you tons of metadata. Pro tip: Don’t forget to look at the EXIF info!
For Log Analysis

When I see a .sqlite file, I use SQLite Browser on Windows. It was not the easiest to learn, but I have always found if I kept clicking around, all the information would be there. As Dory would say if she ran SQLite Browser, “Just keep clicking.”
For the giant text file logs, I use Excel to manage, filter, and sort the data. I know there are more “hacker-ish” methods, but honestly, I get the job done.
For Password Cracking
Just a heads up, this is going to be a longer section. The first things you need to do is identify the hash type. I learned to eyeball this. The article that taught me can be found here.

That being said, I use Cain. I know other people use John the Ripper (which is pre-installed on Kali), but Cain in my personal favorite. It’s a password recovery tool for Windows. It can crack various password hashes by using methods such as dictionary attacks, brute-force, and cryptanalysis attacks. It’s one of my favorite tools for many NCL challenges.
The biggest thing you need to be able to do is to create your own wordlists based on the hints the competition gives you. For some, it’s downloading existing wordlists like the one from the rockyou breach. For others, you might need to download a database of all the Pokemon and their Pokedex number and format it to suit your needs.
As cool as password crackers are, what if you know the password isn’t on your wordlist? For example, what if passwords are made by using NCL, a dash, three letters, another dash, and four numbers (e.g: NCL-ABC-1234)? That’s where Crunch Wordlist Generator comes in. (And it’s pre-installed on that awesome Kali VM you built earlier!)
For Network Capture / .PCAP Files

I use Wireshark or Network Minor.
Wireshark is the most in-depth tool out there for viewing Network Capture Files. Because it’s so in-depth, beginners may have trouble finding what they need. To solve that, learn how to use Wireshark filters and you’ll be an expert in no time!
Network Minor is really great when you need to just get a different perspective on the packet capture. I haven’t found it as useful as Wireshark, but it’s worth having around. If you have a .pcapng file, you won’t be able to open it with the free Network Miner tool. ProTip: You can open it with Wireshark and “Save as” as .pcap.
For Scanning & Enumeration
The How-To Guide I’m going to link to calls NMAP “the god of port scanners used for network discovery and the basis for most security enumeration during the initial stages of penetration testing.” That’s way better than any words I had to describe it. Check out the NMAP Cheat Sheet!
For Cryptography

I saved my favorite section for last! I LOVE Cryptography.
Seriously. My Twitter handle is @CryptoKait.
That being said, don’t get frustrated on this section. Cracking cryptography has always felt like more of an art than a science to me, but I have a few tools that might help.
Black Chamber – Cipher Cracking Tool – Recommended to me when I first started to learn cryptography.
Rumkin Cryptogram Solver – One of my favorite cipher cracking tools. It’s also fantastic for learning how different cipher types function.
Text Tools – ASCII, Hexadecimal, Binary, Octal, and Morse Code Converters. (Will also reverse words and text)
BASE64 – They have ALWAYS had at least one of these and people always struggle to identify it. Use this website. Play with the input charset if you want.
My Macro Tool – I downloaded this forever ago and have adapted it. It helps rearrange and reorganize things if you are manually cracking things like I normally do.
For Anytime You Get Stumped
(And you will…)

Some of you may be laughing right now, but this is the most IMPORTANT tool you have access to during the competition. ANYTIME you are stuck, do a Google Search. Even if you don’t find the answer, you may find something that WILL HELP YOU LATER! Don’t give up. There are answers out there. I know you can find them.
Good Luck!
Let me know what challenges stumped you the most, what tools you found helpful, or what I might be able to add to this list. Feel free to brag a little in the comments if you know a better way! We are all here to learn so I will take any advice you may have to share.
*The views expressed in this post are my own and are in no way affiliated with and do not reflect The National Cyber League, Pace University, or Westchester Community College.

2 thoughts on “My National Cyber League (NCL) Prep-Guide”